Terminology
|
See Deploying AD FS.
The Metadata URL is "https://adfs.example.com/FederationMetadata/2007-06/FederationMetadata.xml", where adfs.example.com is the host of your AD FS server. |
Go to Configuration › System Administration.
Select the "SAML2" tab (if this isn't available, see the 'Availability' info box at the top of this document).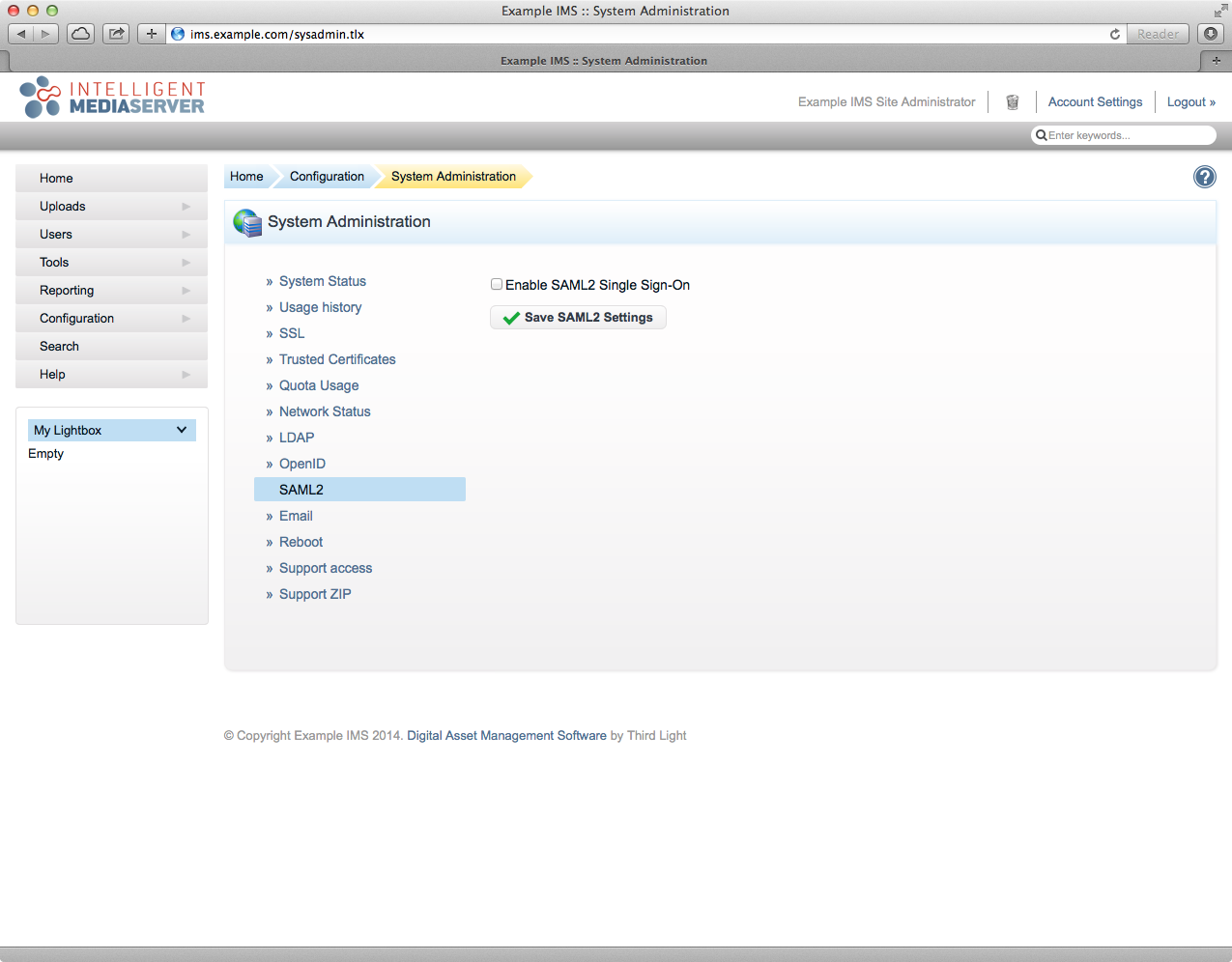
Tick the 'Enable SAML2 Single Sign-On' checkbox, this will reveal the SAML2 configuration fields.
If your IMS server can access your AD FS server:
IMS will automatically load the Metadata from the URL that you provide and check for updates once a day. |
Ensure the "Load IdP Metadata from URL" radio option is selected.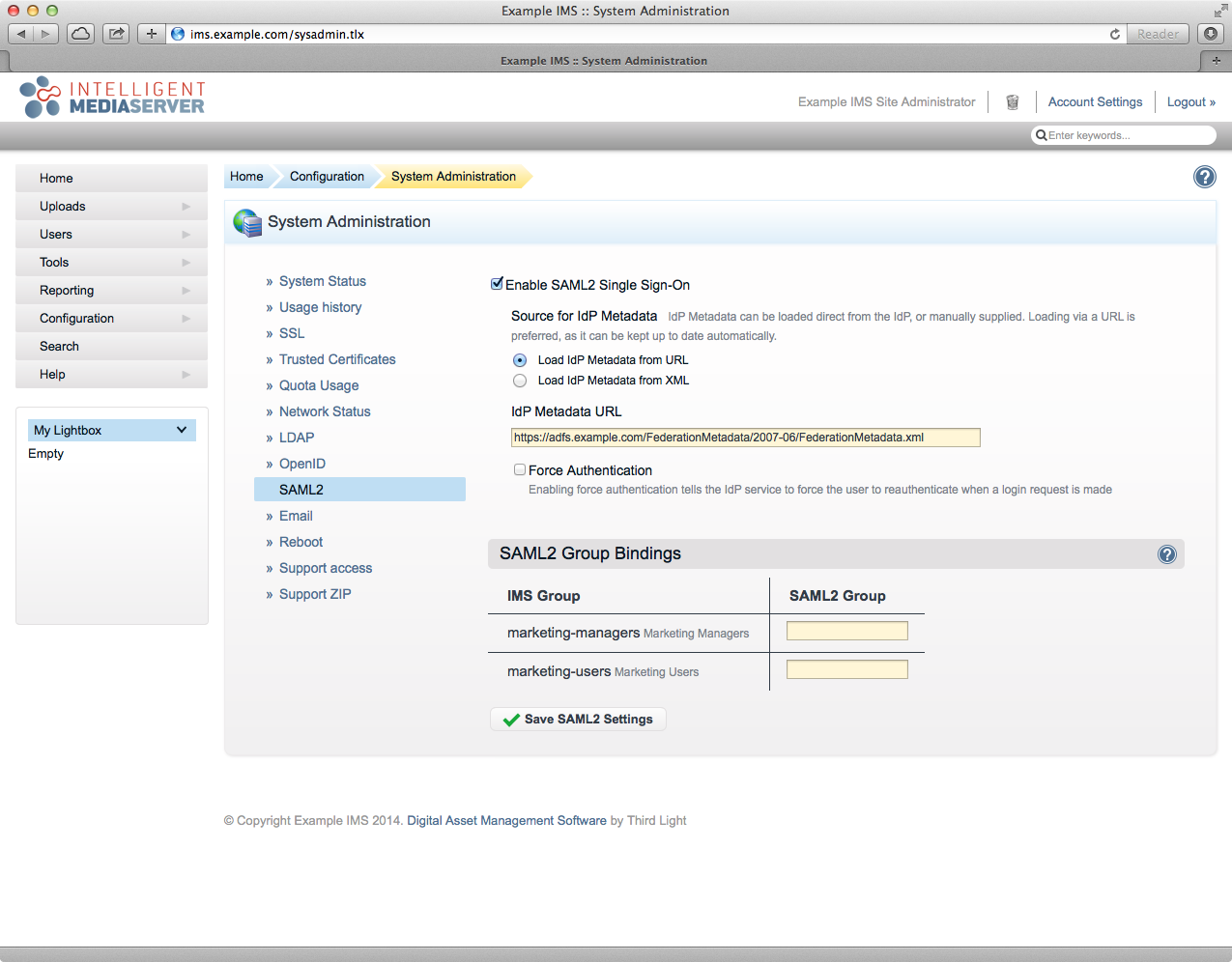
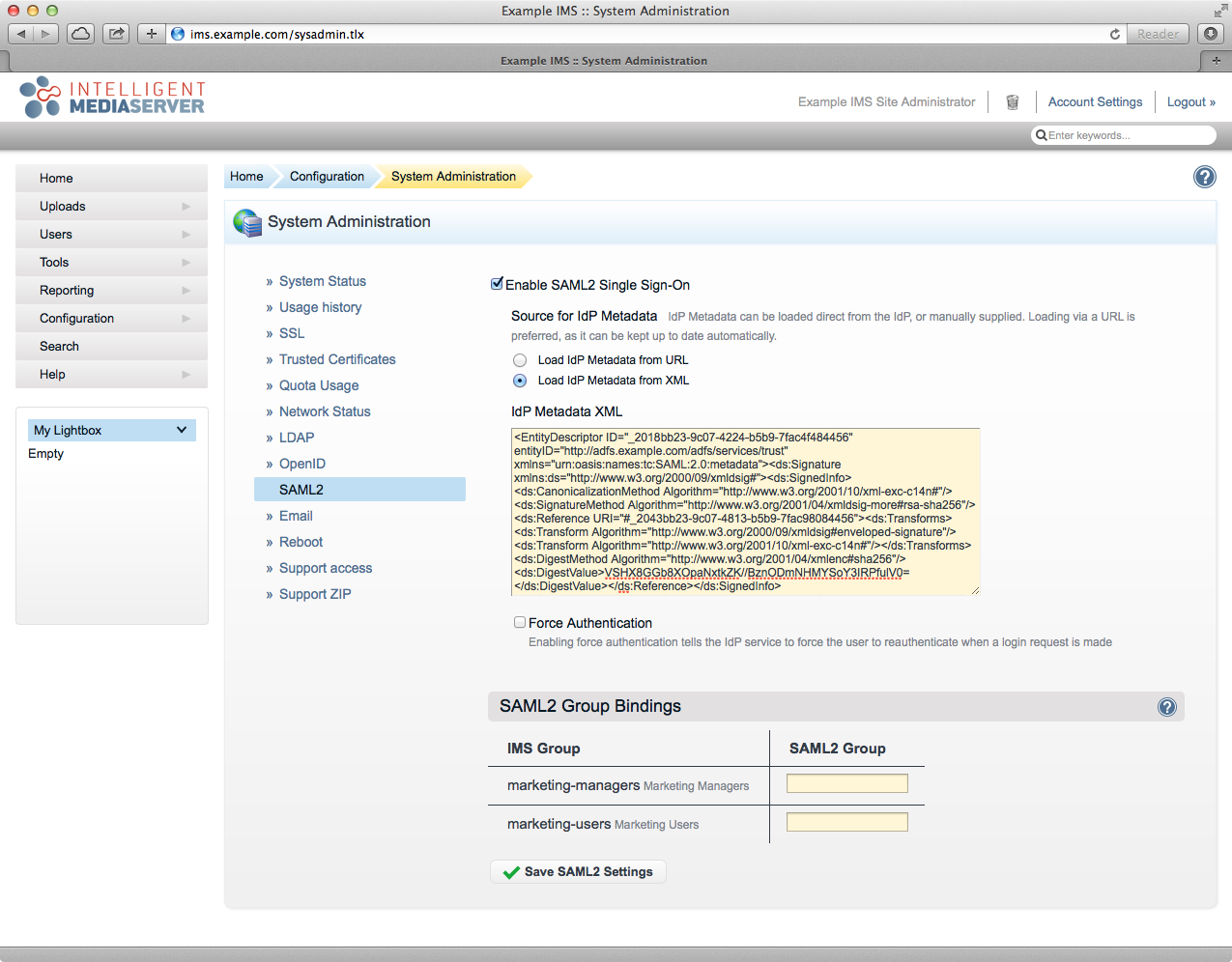
If your IMS server cannot access your AD FS server:
IMS will not automatically update the Metadata if you change your AD FS configuration. If you make any changes, then you may have to re-add the Metadata manually (as below). |
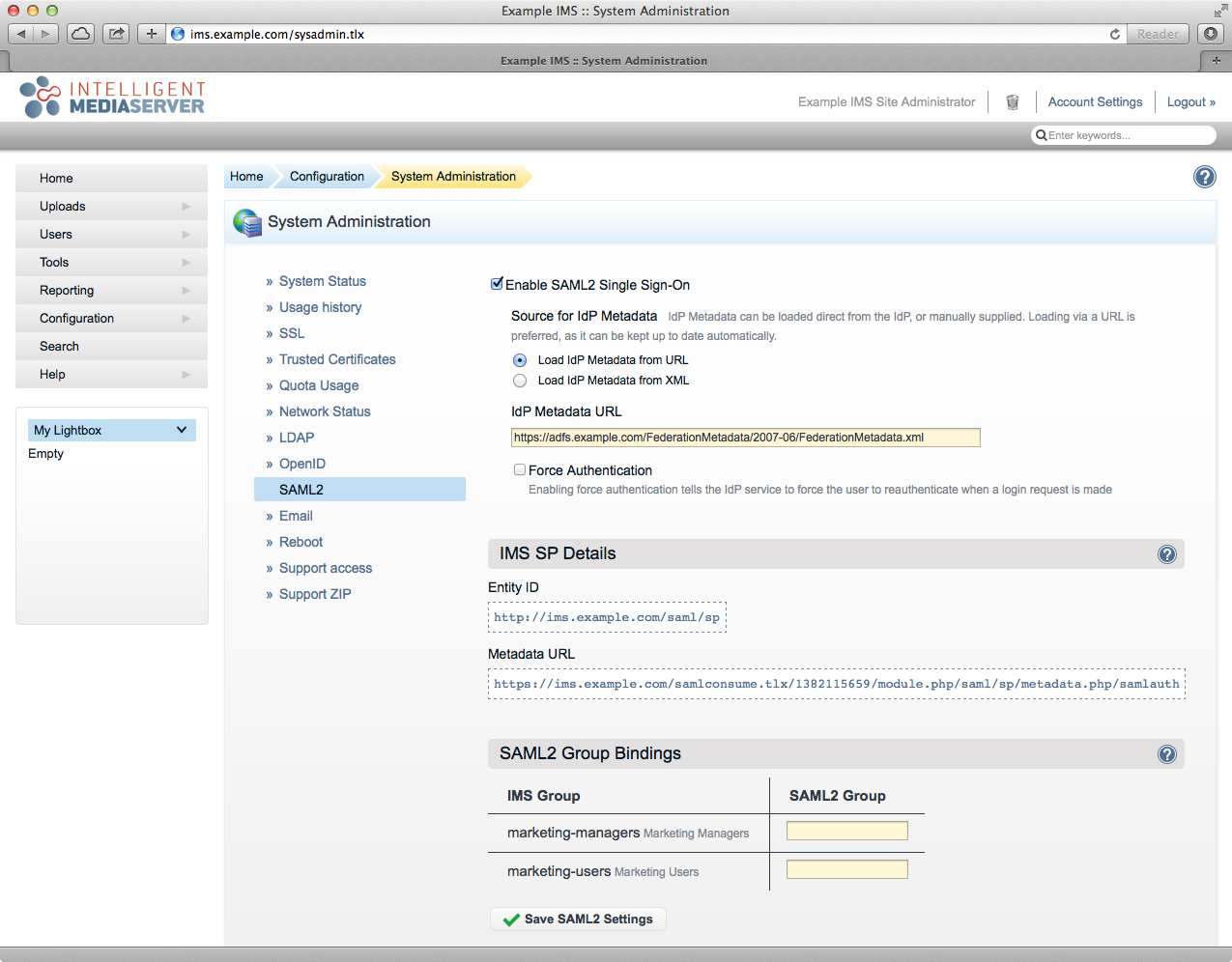
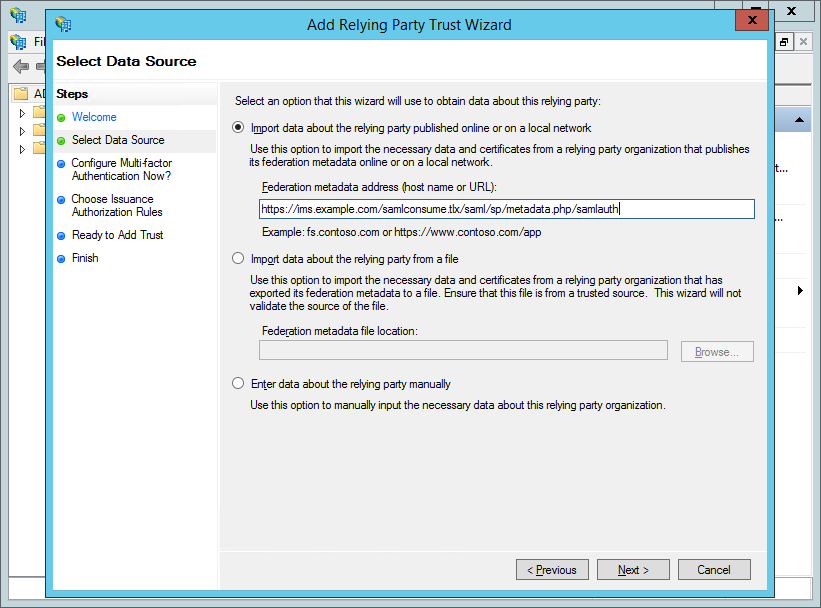
Note that there there is now an Entity ID and Metadata URL for the SP (e.g. https://ims.example.com/samlconsume.tlx/1382115659/module.php/saml/sp/metadata.php/samlauth). Keep note of this as you will need it to configure the Relying Party in AD FS, below.
Open AD FS Management from Administrative Tools.
Right-click the top-level "AD FS" folder.
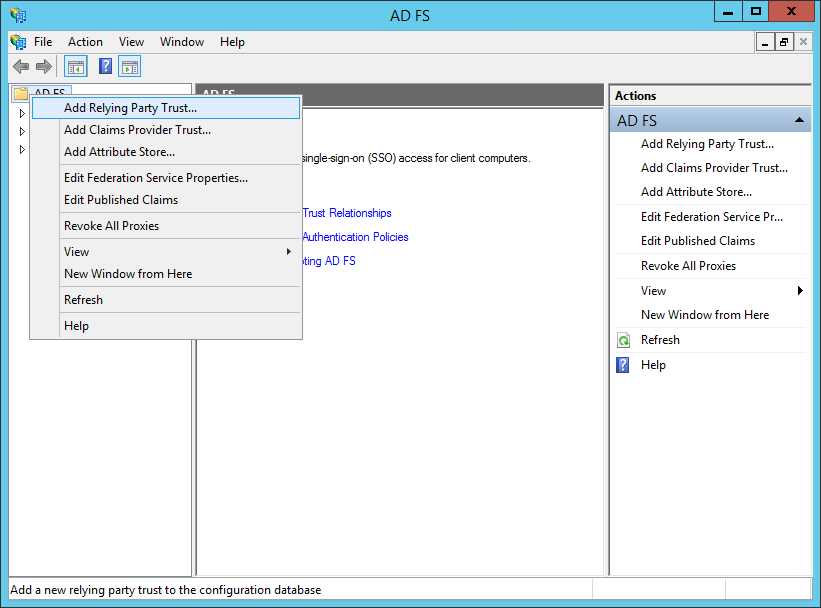
Select "Add Relying Party Trust…".
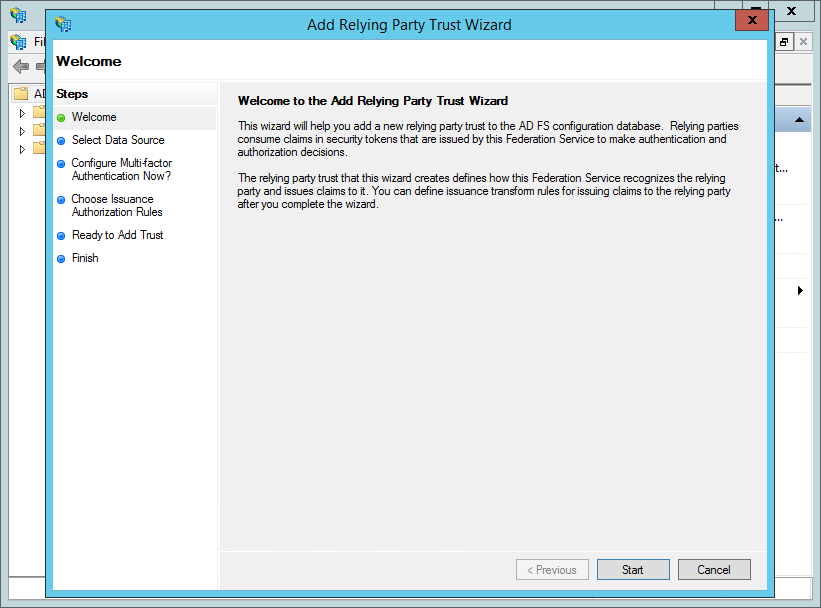
Click "Start".
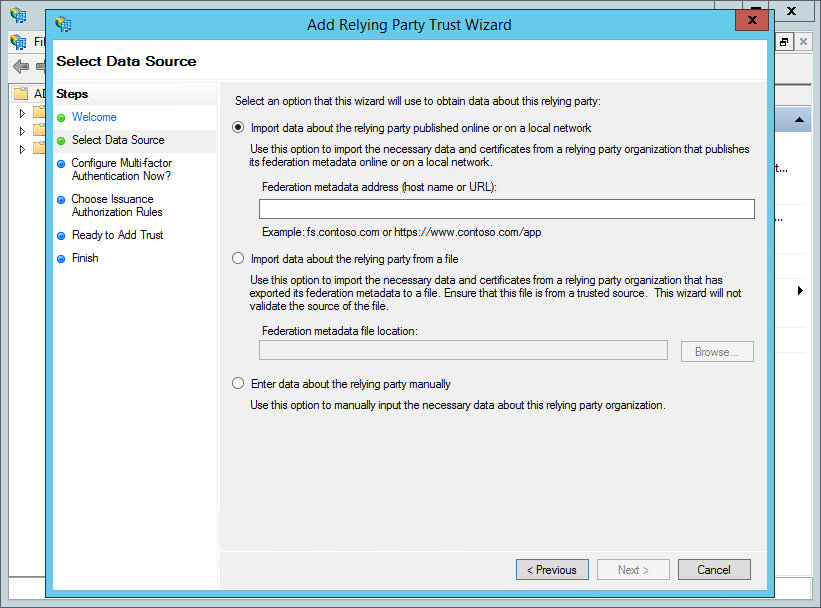
If your AD FS server can directly access IMS, then:
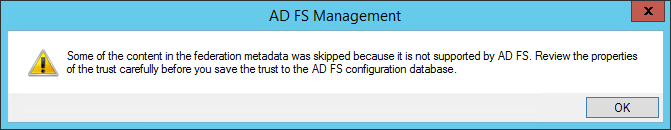
If your AD FS server cannot directly access IMS, then:Click "Next".
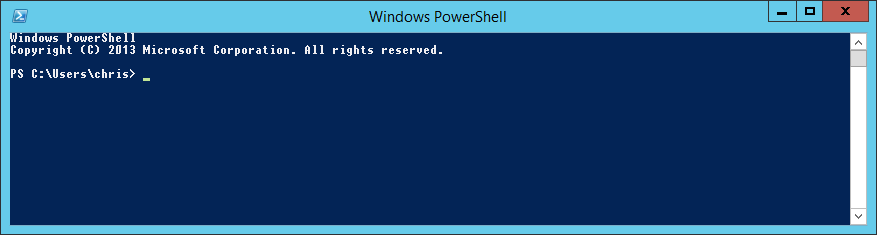
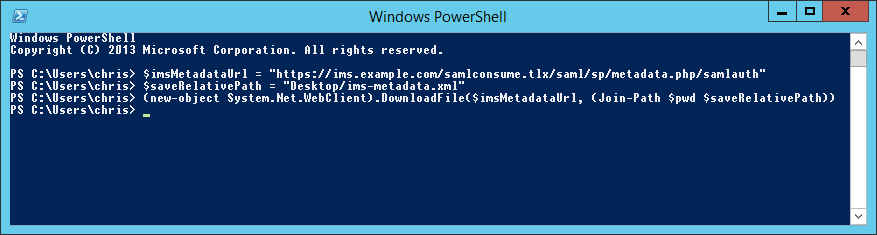
Run the following command (change the URL on the first line to the value of the Metadata URL for IMS and '1234567890' to the Id specific for your installation).
$imsMetadataUrl = "https://ims.example.com/samlconsume.tlx/1234567890/module.php/saml/sp/metadata.php/samlauth" $saveRelativePath = "Desktop/ims-metadata.xml" (new-object System.Net.WebClient).DownloadFile($imsMetadataUrl, (Join-Path $pwd $saveRelativePath)) |
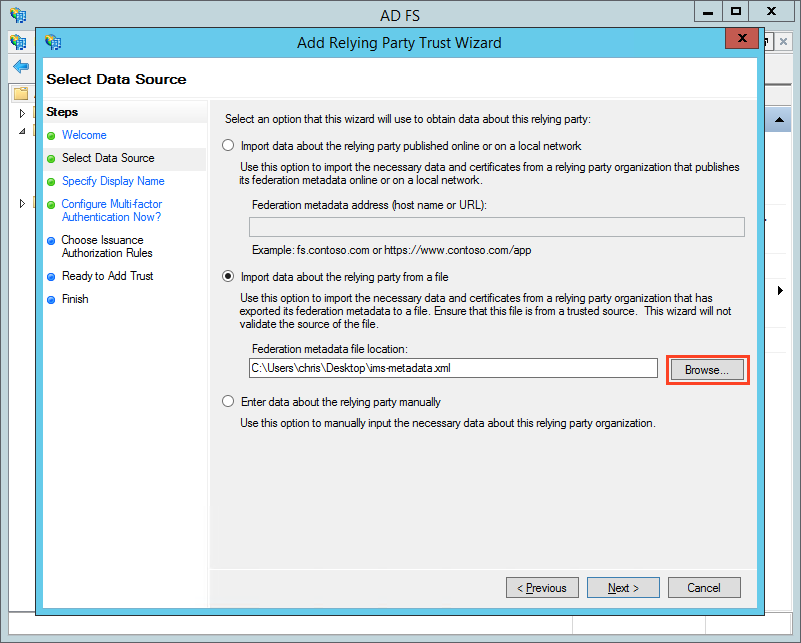
Click Next.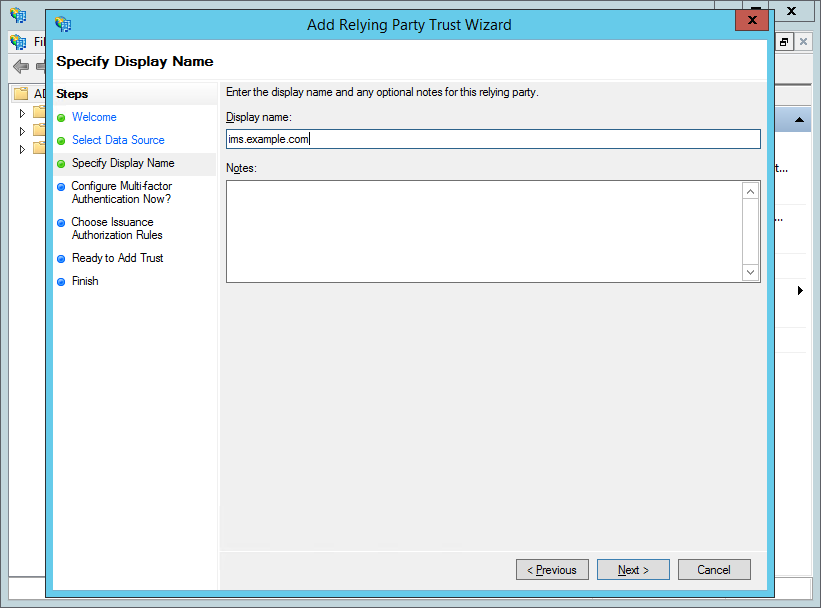
Enter a "Display name" (e.g. "ims.example.com"; the name that Relying Party will appear in the AD FS management tool) and, optionally, add some "Notes". Click "Next".
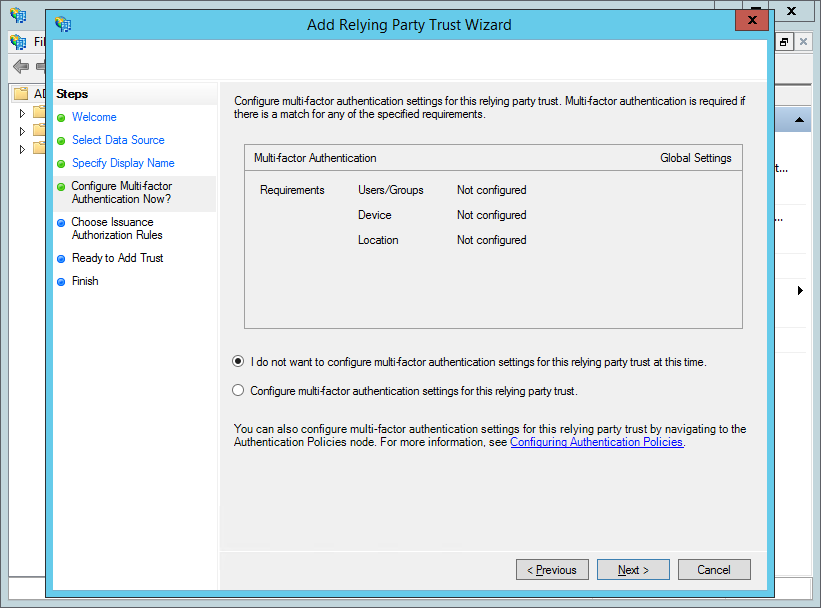
Click "Next".
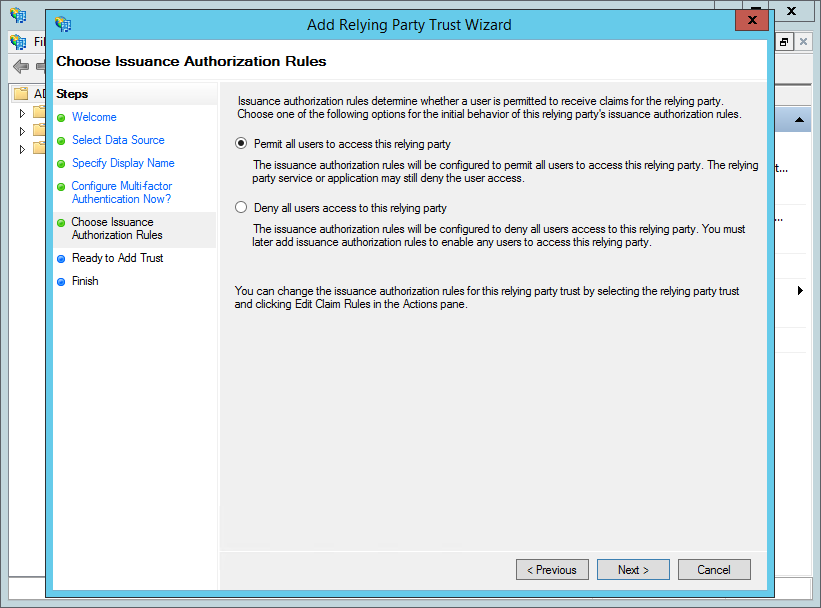
Click "Next".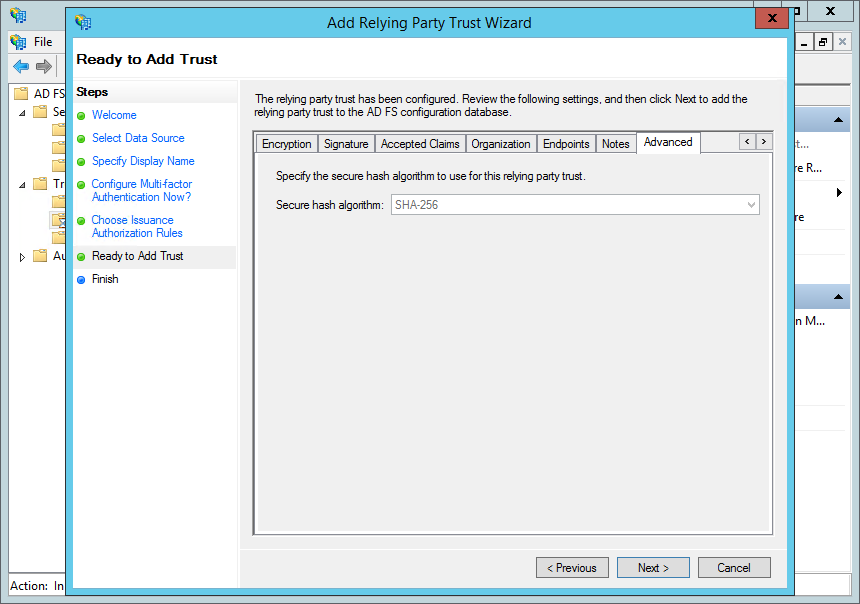
Click "Next".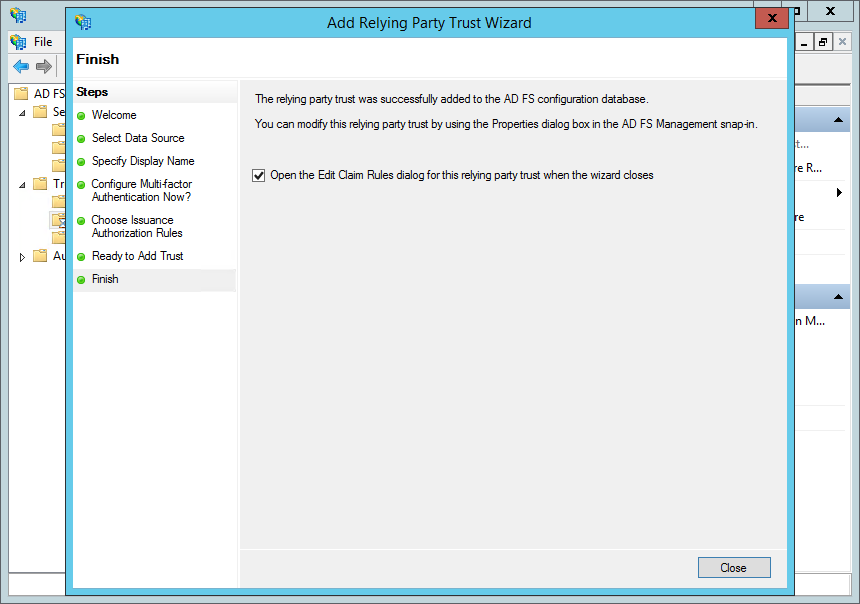
Ensure that "Open the Edit Claim Rules dialog for this relying party trust when the wizard closes" is checked. Click "Close".
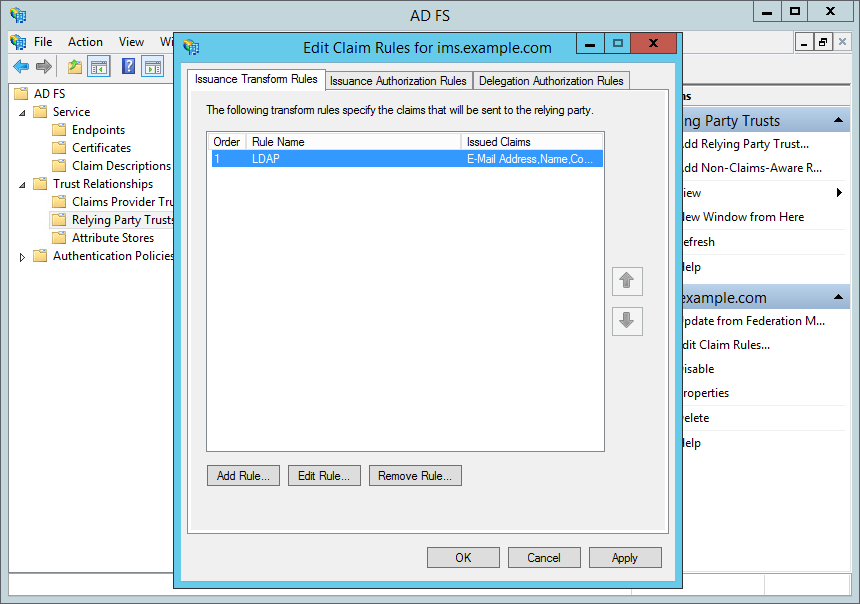
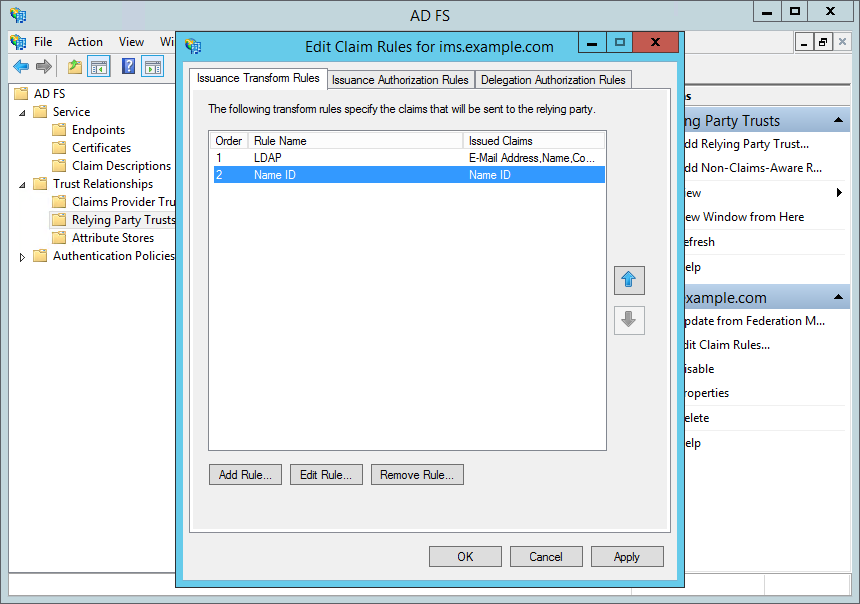
Note: You can also get to this by right-clicking on the IMS Relying Party (e.g. ims.example.com) and selecting "Edit Claim Rules…".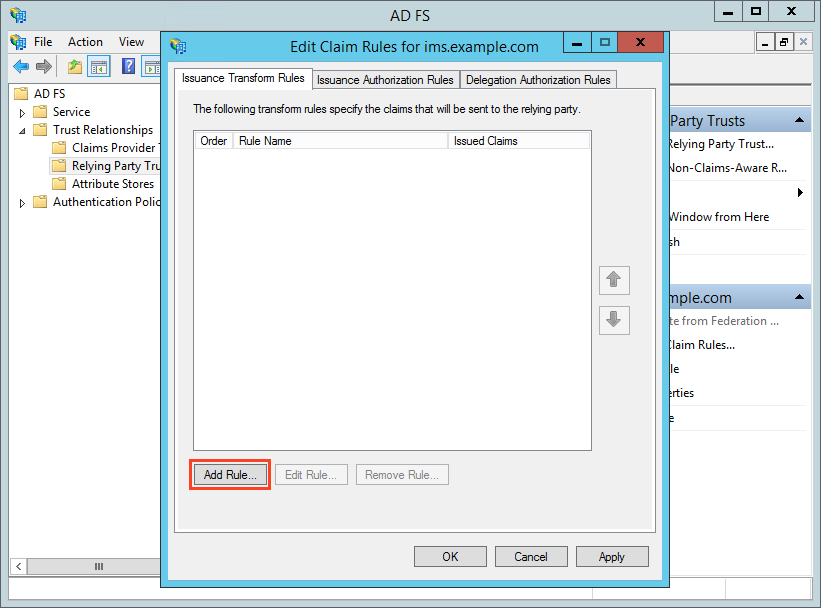
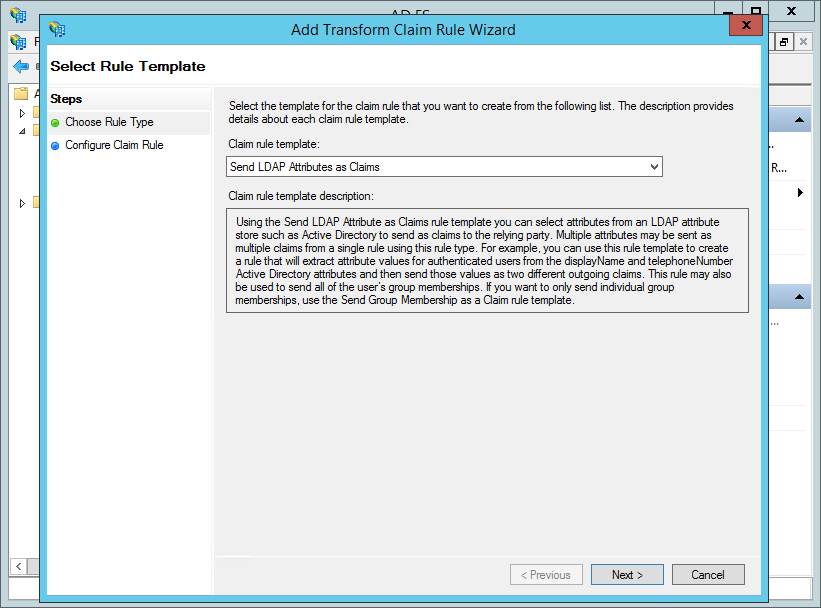
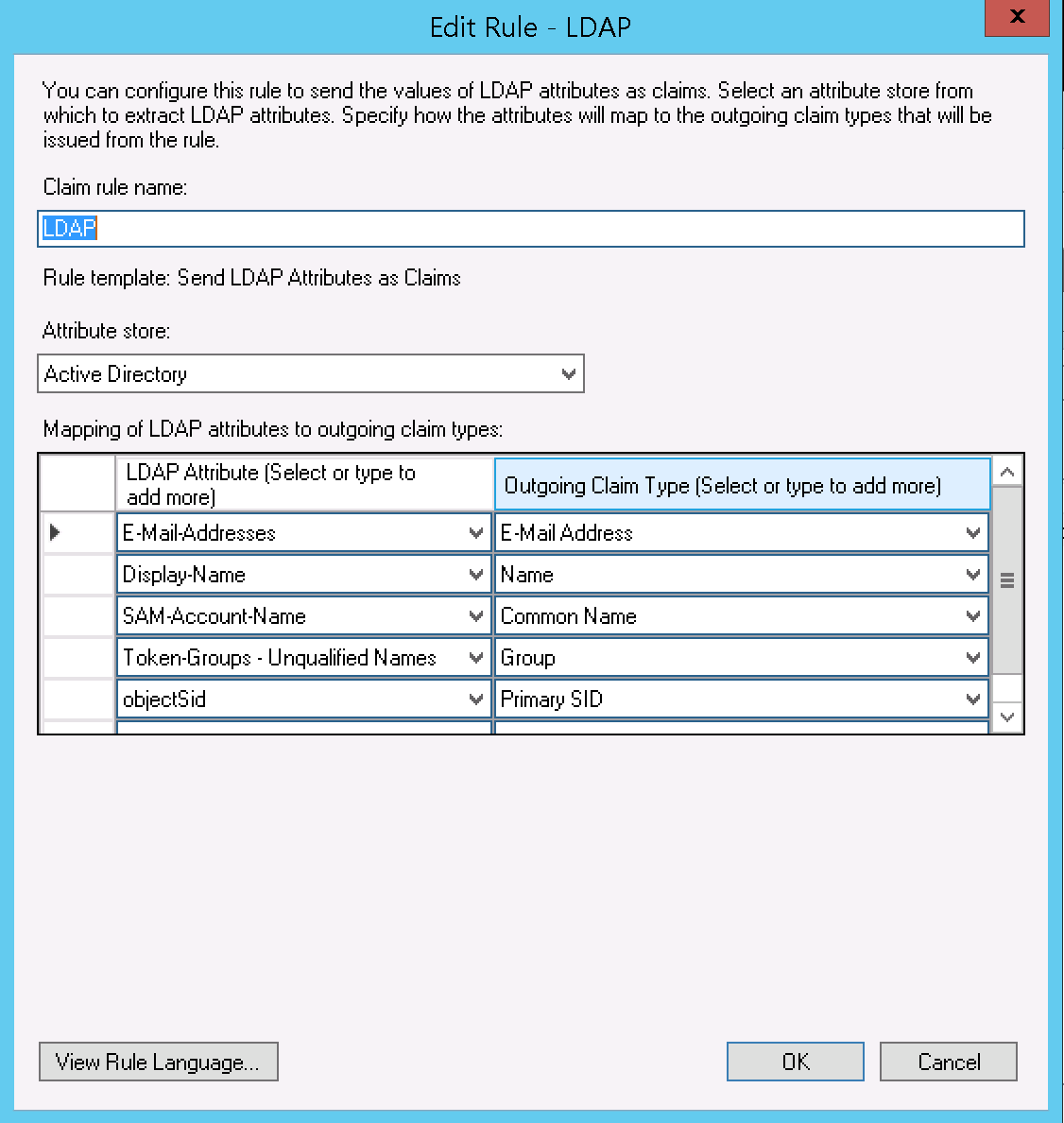
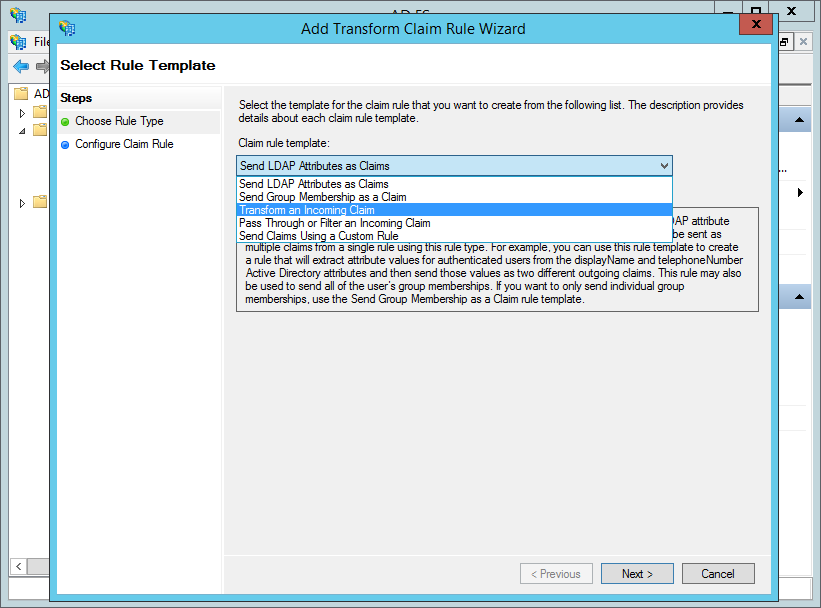
"Mapping of LDAP attributes to outgoing claim types", as follows (note: the "Associated Claim Type URI" is configured in AD FS > Service > Claim Descriptions, and these should be provided by a default AD FS install).
| LDAP Attribute | Outgoing Claim Type | Associated Claim Type URI | Purpose in IMS |
|---|---|---|---|
| E-Mail-Addresses | E-Mail Address | http://schemas.xmlsoap.org/ws/2005/05/identity/claims/emailaddress | Email Address - also used to find users where the authentication type has changed to SAML2 |
| Display-Name | Name | http://schemas.xmlsoap.org/ws/2005/05/identity/claims/name | Description - updated on login |
| SAM-Account-Name | Common Name | http://schemas.xmlsoap.org/claims/CommonName | Username - only used at initial creation |
| Token-Groups - Unqualified Names | Group | http://schemas.xmlsoap.org/claims/Group
| Group mapping - updated on login |
| objectSid | Primary SID | http://schemas.microsoft.com/ws/2008/06/identity/claims/primarysid | Generation of Name ID (see next rule) - used to identify bound users |
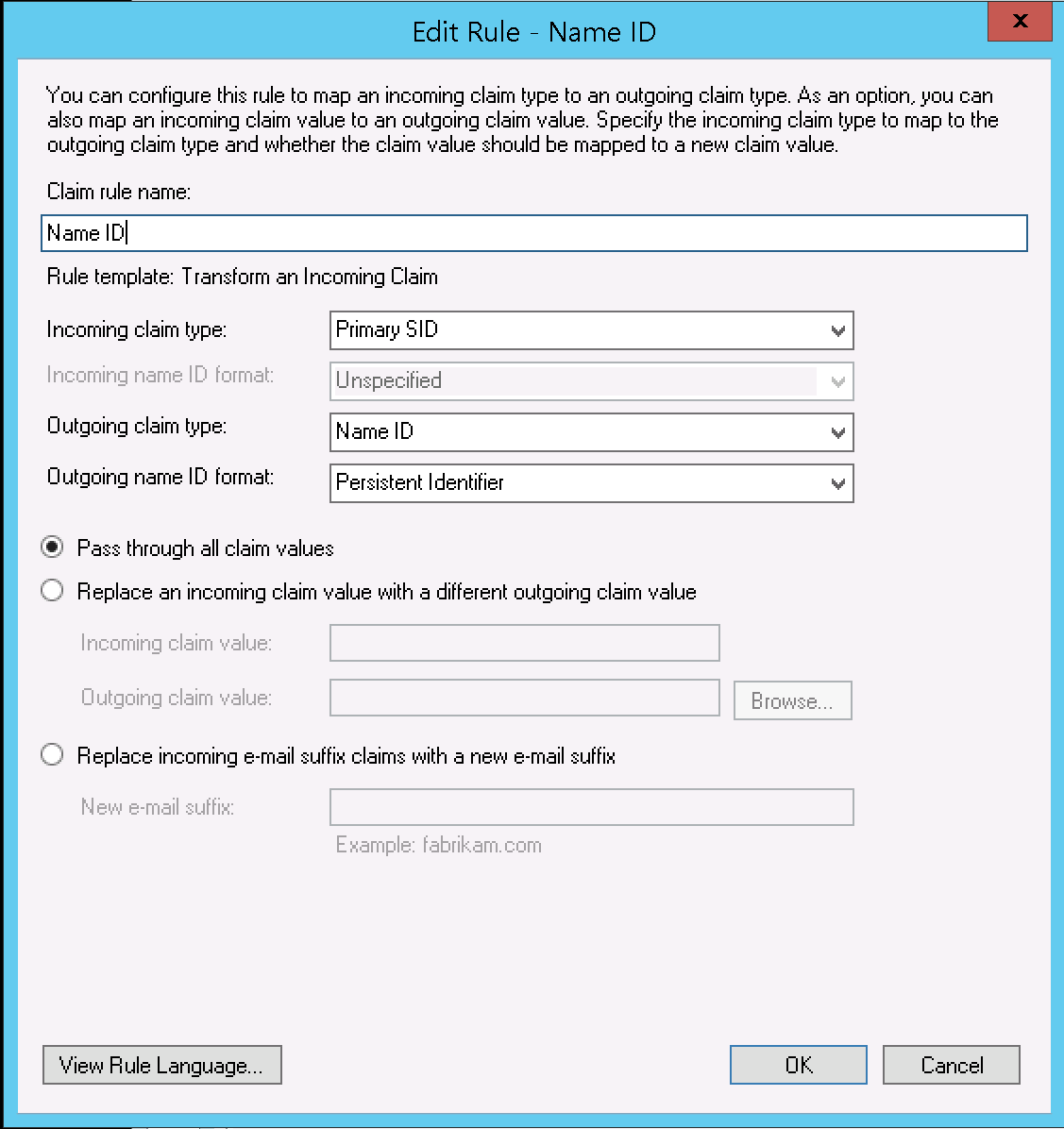
In the above, objectSid is used as the basis for generating a Name ID. You can use other fields - objectGuid being one suitable example. You should normally avoid using sAMAccountName / email / User Principal Name for this as they may change.
IMS and AD FS should now both be configured for Single-Sign-On. To quickly test:
Open up IMS in your browser (e.g. http://ims.example.com)
If you're logged in, then logout.
Go to libraryhome.tlx (e.g. http://ims.example.com/libraryhome.tlx).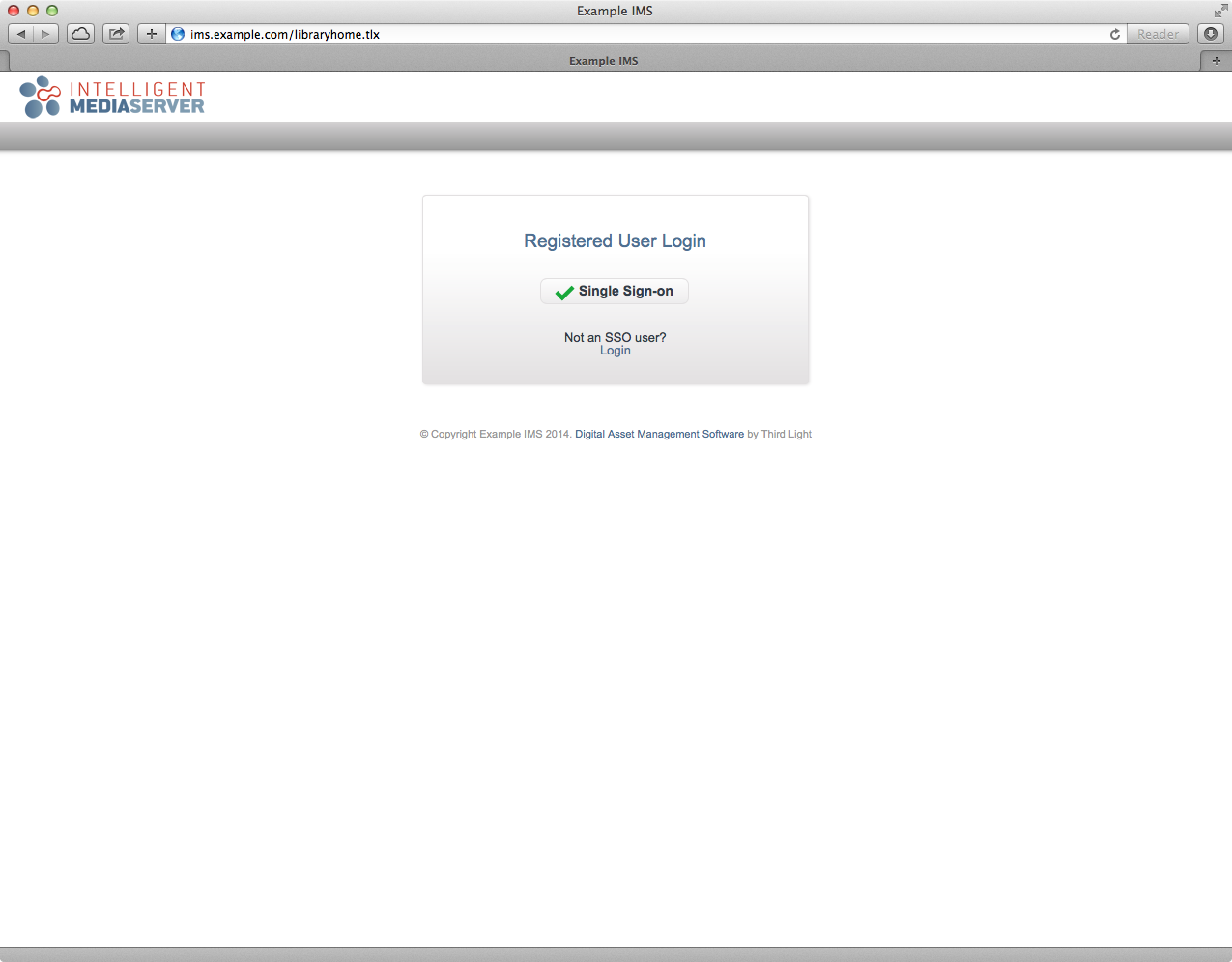
Click the "Login with SSO" button.
You should automatically be authenticated via AD FS.
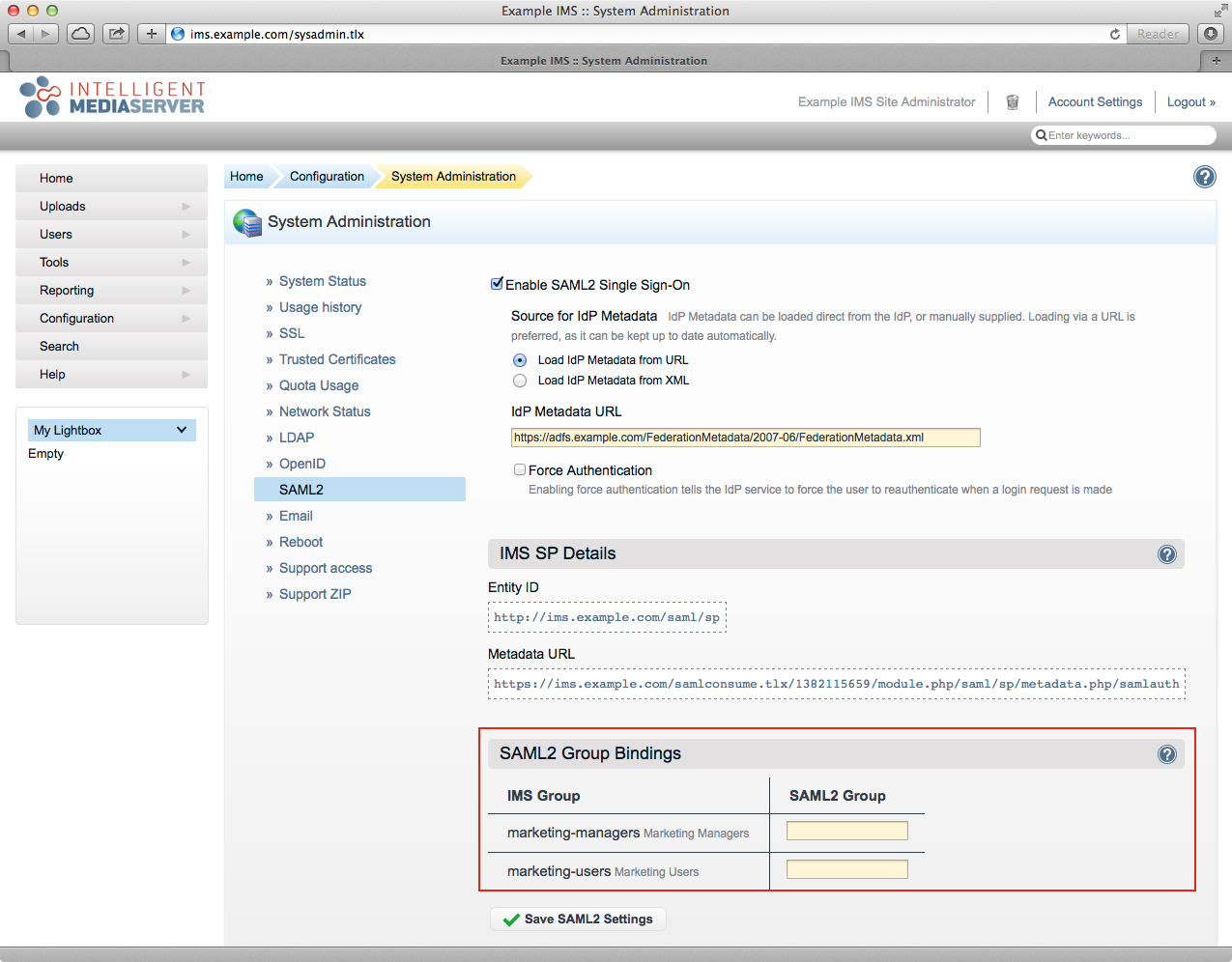
When a user first accesses IMS using AD FS for authentication a new IMS user will be created using the Auto User Preset and associated with their AD FS account (this is based on the value returned for the Name ID). Alternatively, the SAML2 Group Bindings (red box, above) enables placing a user in an IMS group based on their AD FS group membership (the "IMS Group" is the name of the group in IMS and the "SAML2 Group" allows you to enter the group name provided from AD FS). When using this feature, it is important to understand the following caveats:
If you have replaced the token-signing certificate on your ADFS server, the existing metadata on the IMS system will need to be refreshed to restore external authentication. Simply re-save your SAML2 configuration inside IMS to do this.