...
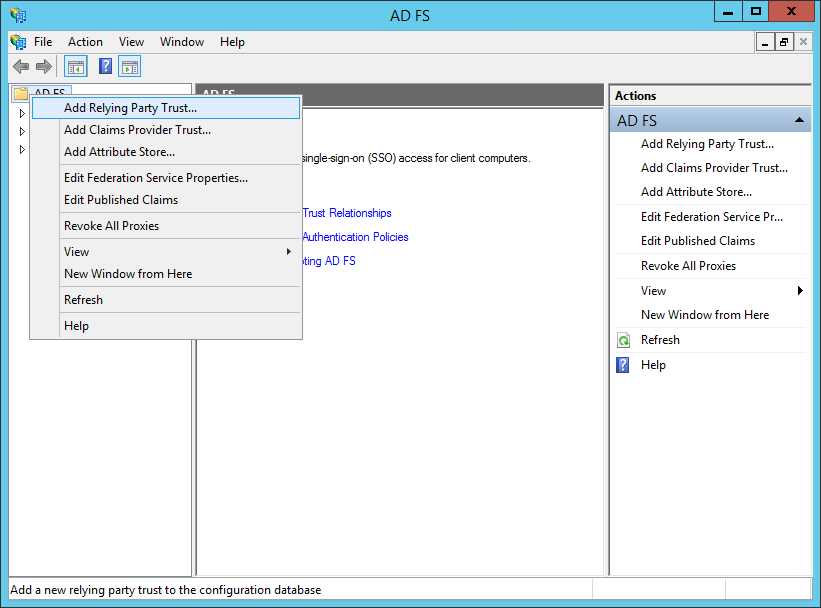
Open AD FS Management from Administrative Tools.
Right-click the top-level "AD FS" folder.
Select "Add Relying Party Trust…".
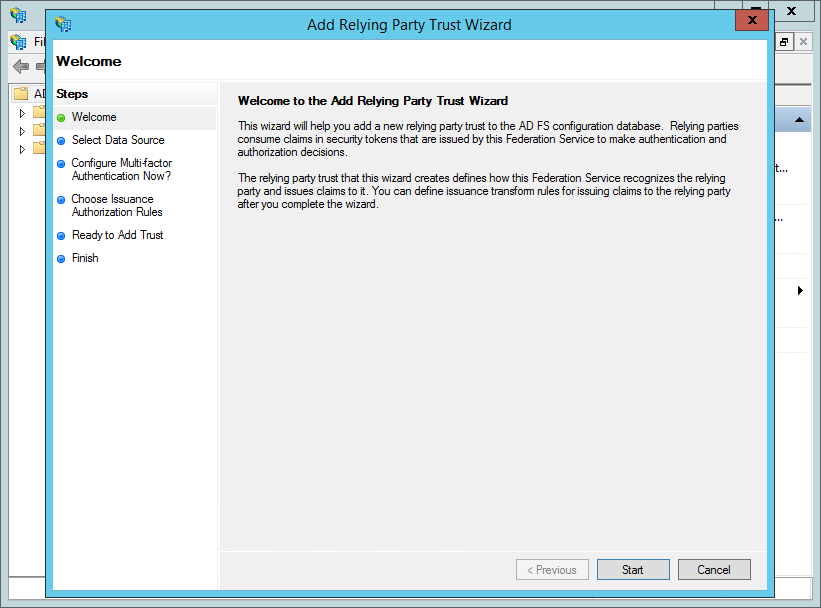
Click "Start".
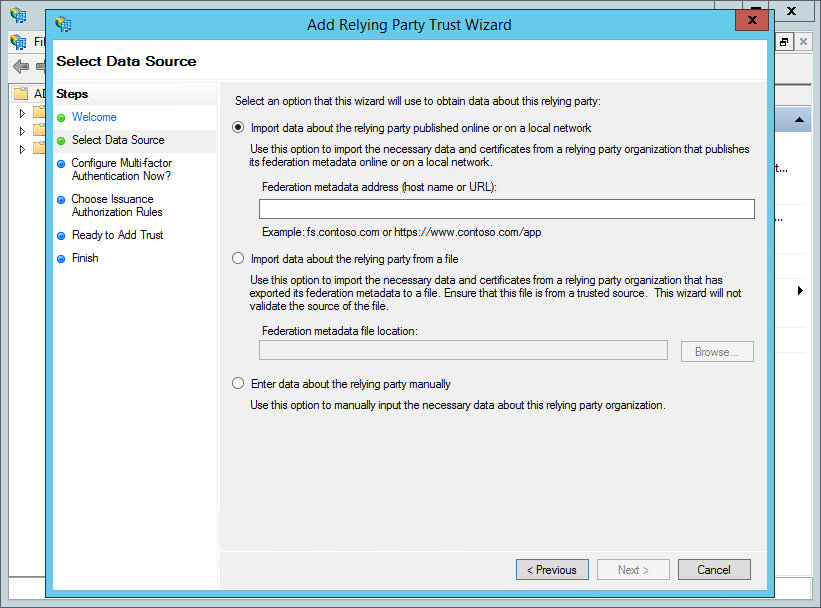
If your AD FS server can directly access IMS, then:
- Enter the Metadata URL for the IMS SP in the field labelled "Federation metadata address (host name or URL)".
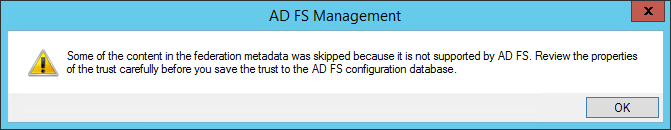
- If you get a warning (screenshot below), you can ignore this by clicking "OK".
- If you get an error "AD FS could not create ssl/tls secure channel", this may indicate that your AD FS server does not support TLSv1.2. See the Microsoft documentation to enable this - at the time of writing, this can be found at https://docs.microsoft.com/en-us/windows-server/identity/ad-fs/operations/manage-ssl-protocols-in-ad-fs#enable-and-disable-tls-12
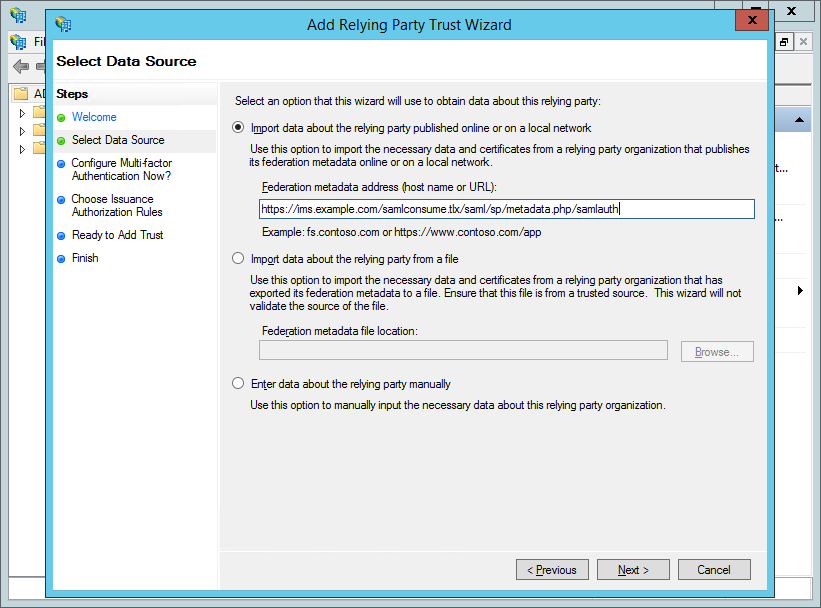
- Enter the Metadata URL for the IMS SP in the field labelled "Federation metadata address (host name or URL)".
If your AD FS server cannot directly access IMS, then:Click "Next".
- You will need to download the SPMetadata from IMS into a file and get this onto the AD FS server. For example:
- Open a new Powershell Window
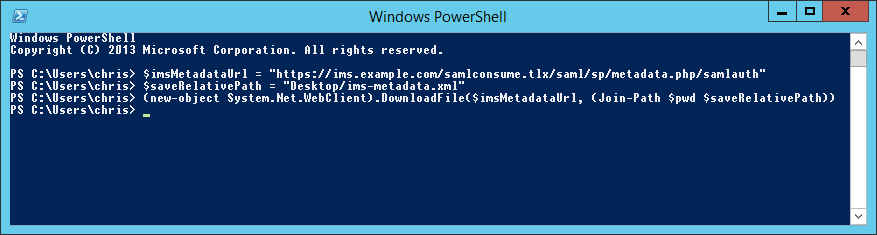
Run the following command (change the URL on the first line to the value of the Metadata URL for IMS and '1234567890' to the Id specific for your installation).
Code Block language powershell $imsMetadataUrl = "https://ims.example.com/samlconsume.tlx/1234567890/module.php/saml/sp/metadata.php/samlauth" $saveRelativePath = "Desktop/ims-metadata.xml" (new-object System.Net.WebClient).DownloadFile($imsMetadataUrl, (Join-Path $pwd $saveRelativePath))
- Open a new Powershell Window
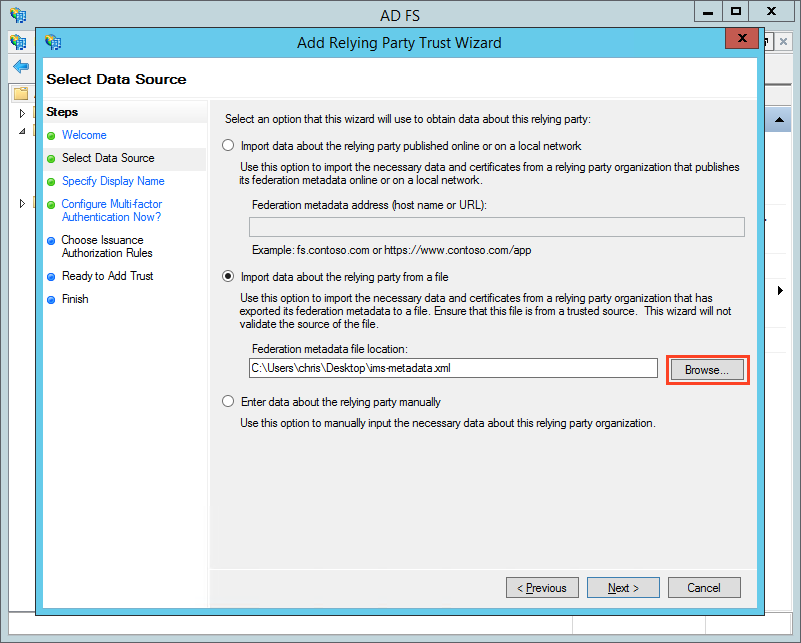
- Click the radio button to the left of "Import data about the relying party from a file".
- Click "Browse" (highlighted in red, above) and choose the location of IMS's SP Metadata that you downloaded.
- You will need to download the SPMetadata from IMS into a file and get this onto the AD FS server. For example:
Click Next.
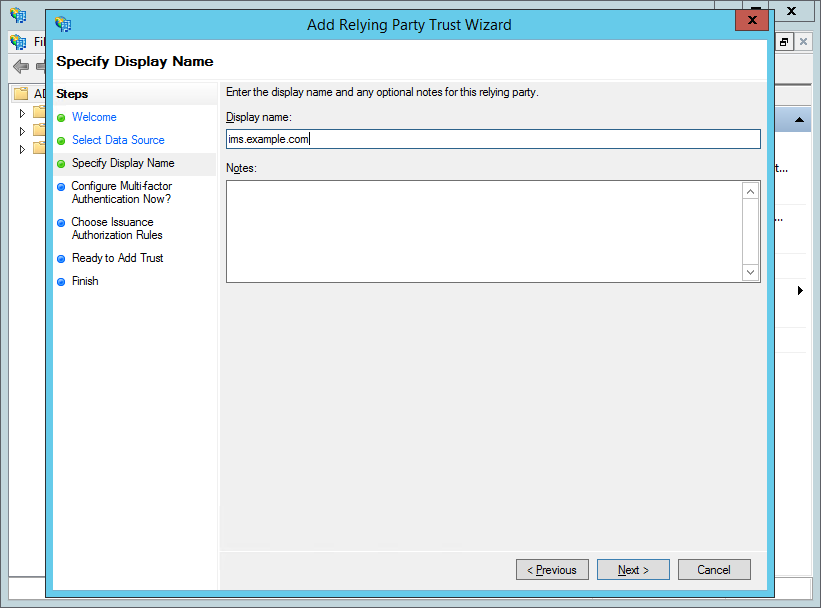
Enter a "Display name" (e.g. "ims.example.com"; the name that Relying Party will appear in the AD FS management tool) and, optionally, add some "Notes". Click "Next".
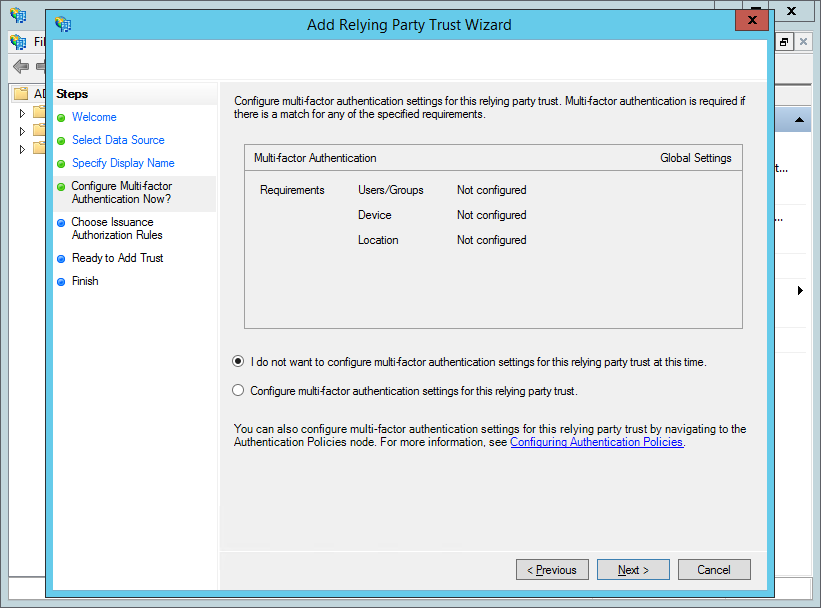
Click "Next".
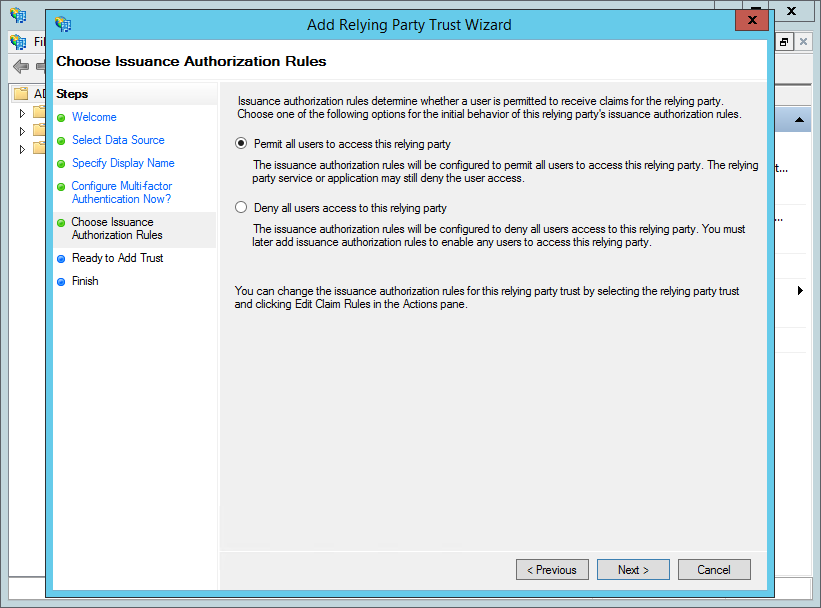
Click "Next".
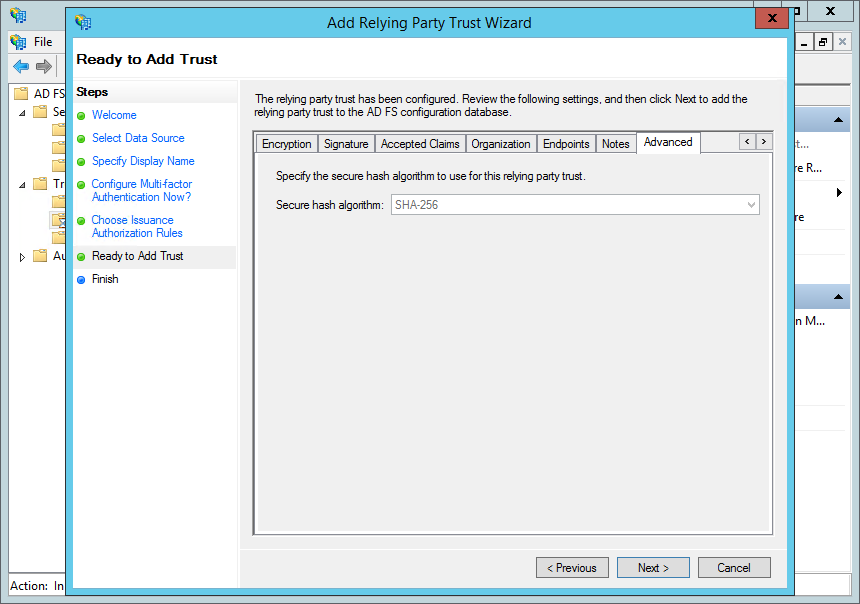
Click "Next".
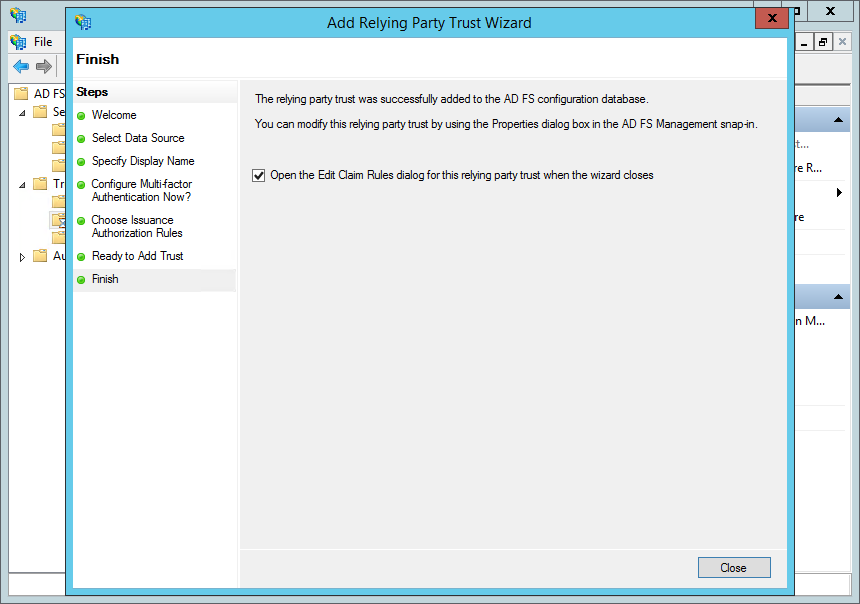
Ensure that "Open the Edit Claim Rules dialog for this relying party trust when the wizard closes" is checked. Click "Close".
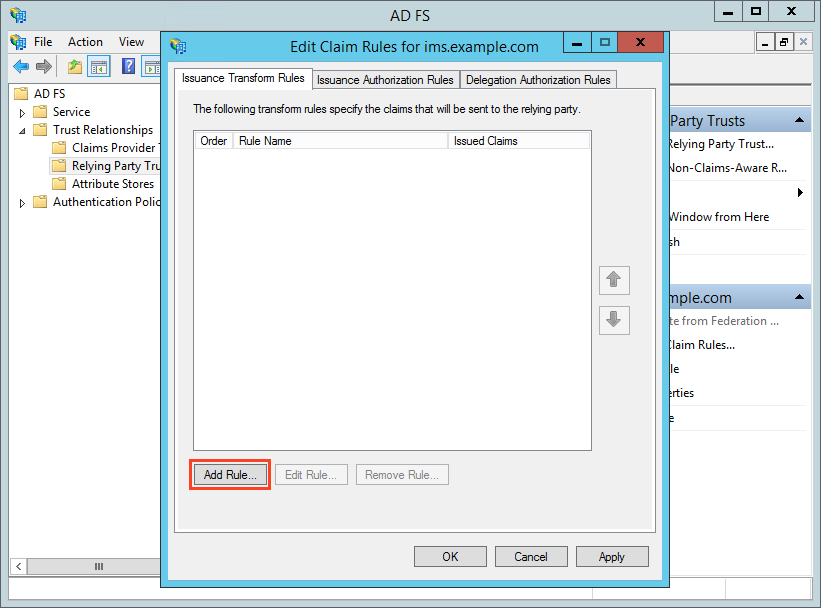
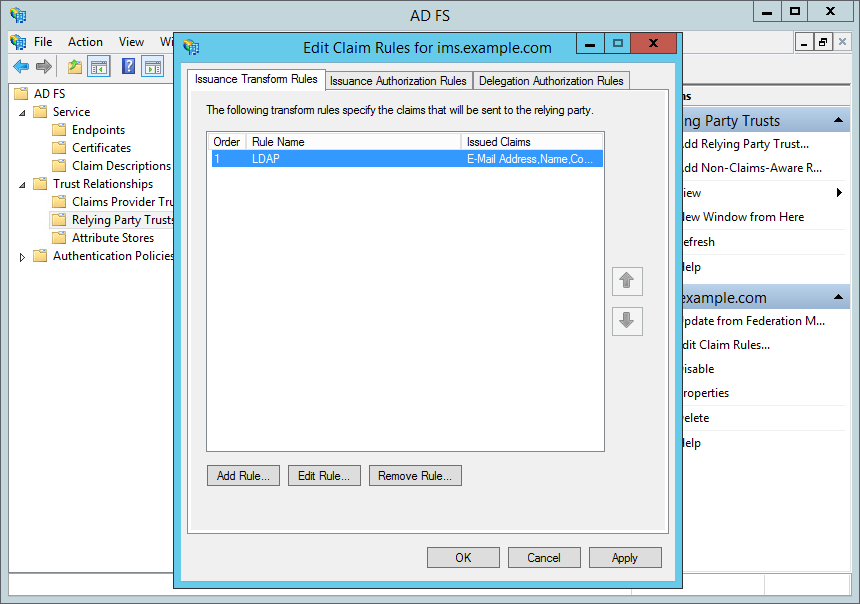
Note: You can also get to this by right-clicking on the IMS Relying Party (e.g. ims.example.com) and selecting "Edit Claim Rules…".- Click "Add Rule…" (highlighted in red, above).
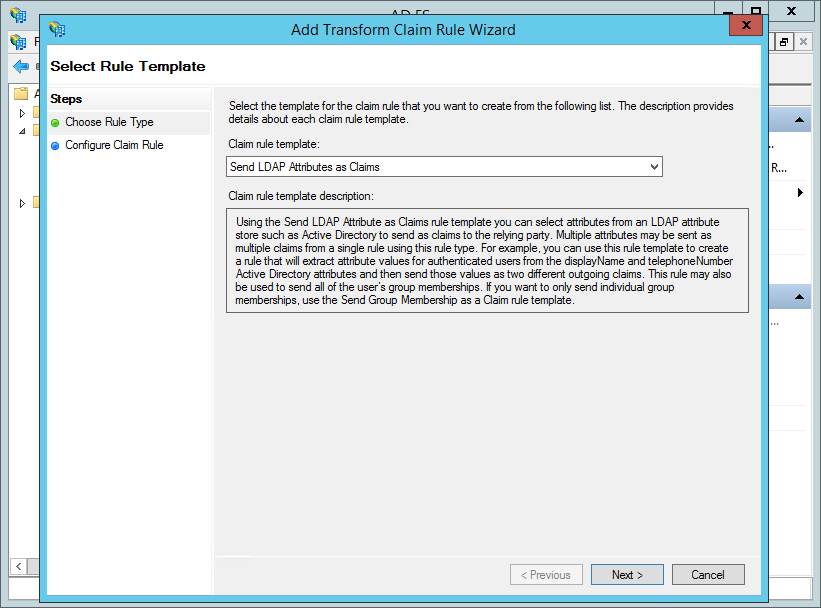
- Leave the "Claim rule template" as "Send LDAP Attributes as Claims" and click "Next".
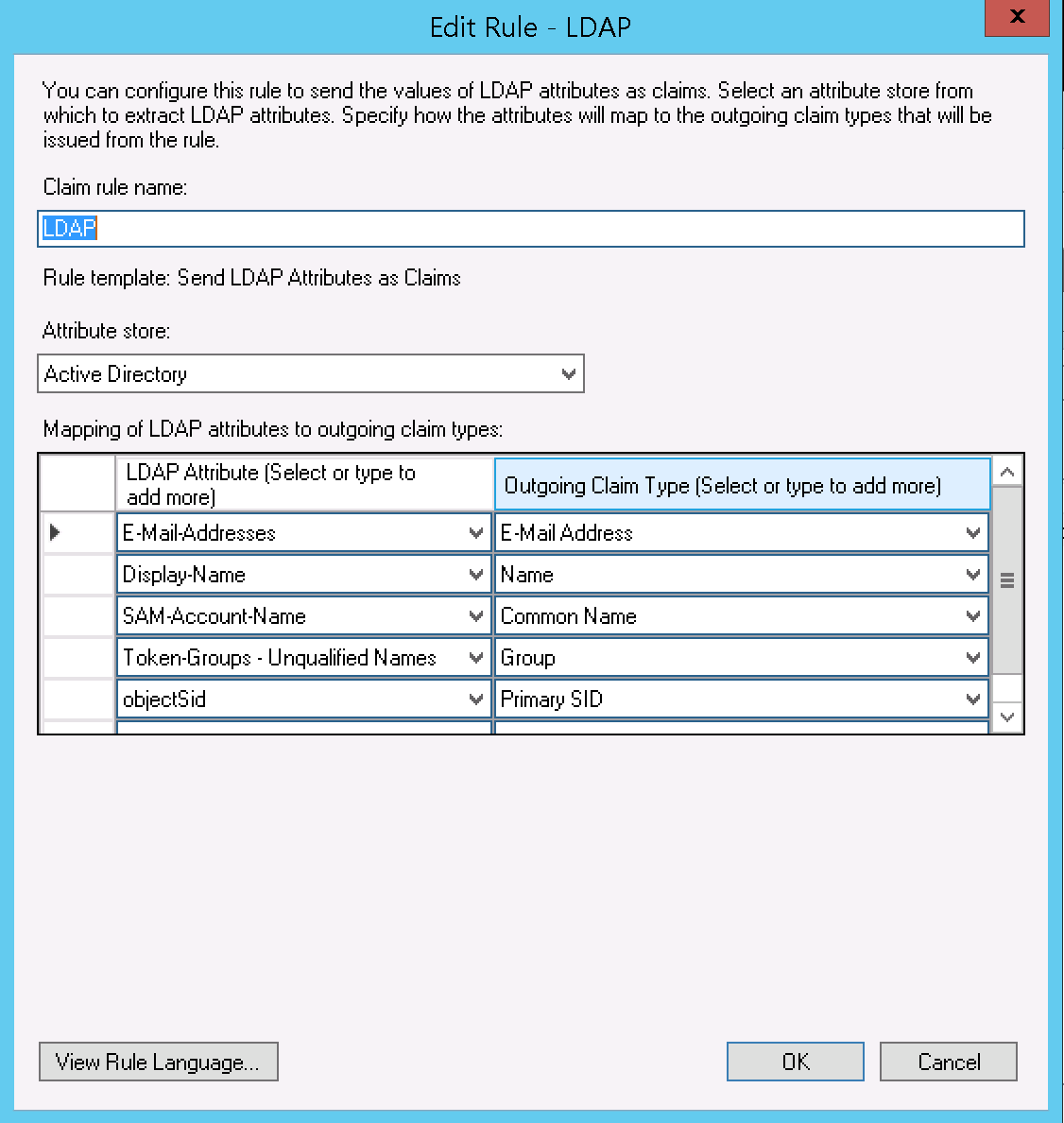
- Complete the form, as follows:
- "Claim rule name" (highlighted in red, above): "LDAP"
- "Attribute store" (navy): select "Active Directory"
"Mapping of LDAP attributes to outgoing claim types" (green), as follows (note: the "Associated Claim Type URI" is configured in AD FS > Service > Claim Descriptions, and these should be provided by a default AD FS install).
LDAP Attribute Outgoing Claim Type Associated Claim Type URI Purpose in IMS E-Mail-Addresses E-Mail Address http://schemas.xmlsoap.org/ws/2005/05/identity/claims/emailaddressEmail Address - also used to find users where the authentication type has changed to SAML2 Display-Name Name http://schemas.xmlsoap.org/ws/2005/05/identity/claims/nameDescription - updated on login SAM-Account-Name Common Name http://schemas.xmlsoap.org/claims/CommonNameUsername - only used at initial creation Token-Groups - Unqualified Names Group http://schemas.xmlsoap.org/claims/GroupGroup mapping - updated on login objectSid Primary SID http://schemas.microsoft.com/ws/2008/06/identity/claims/primarysidGeneration of Name ID (see next rule) - used to identify bound users
- Click "Finish".
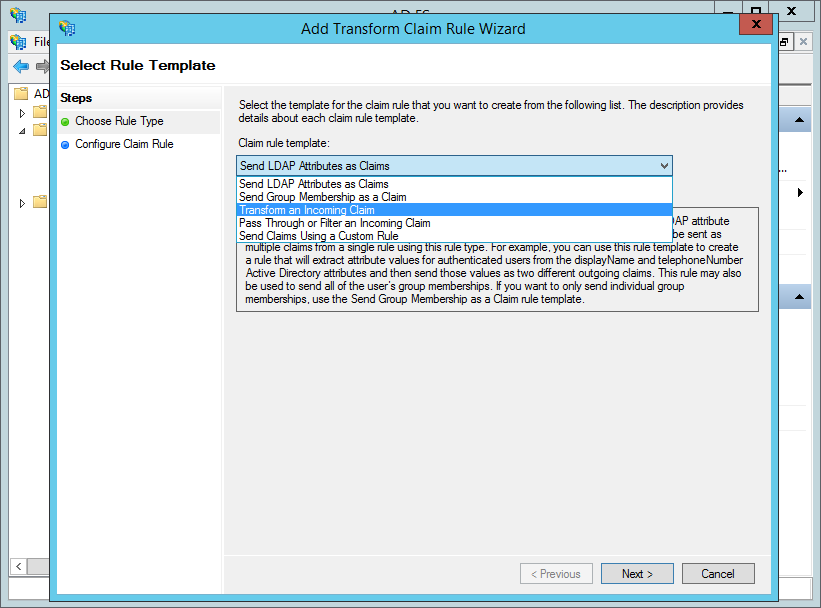
- Click "Add Rule…" again.
- Select "Transform an Incoming Claim" from the "Claim rule template"
- Click "Next".
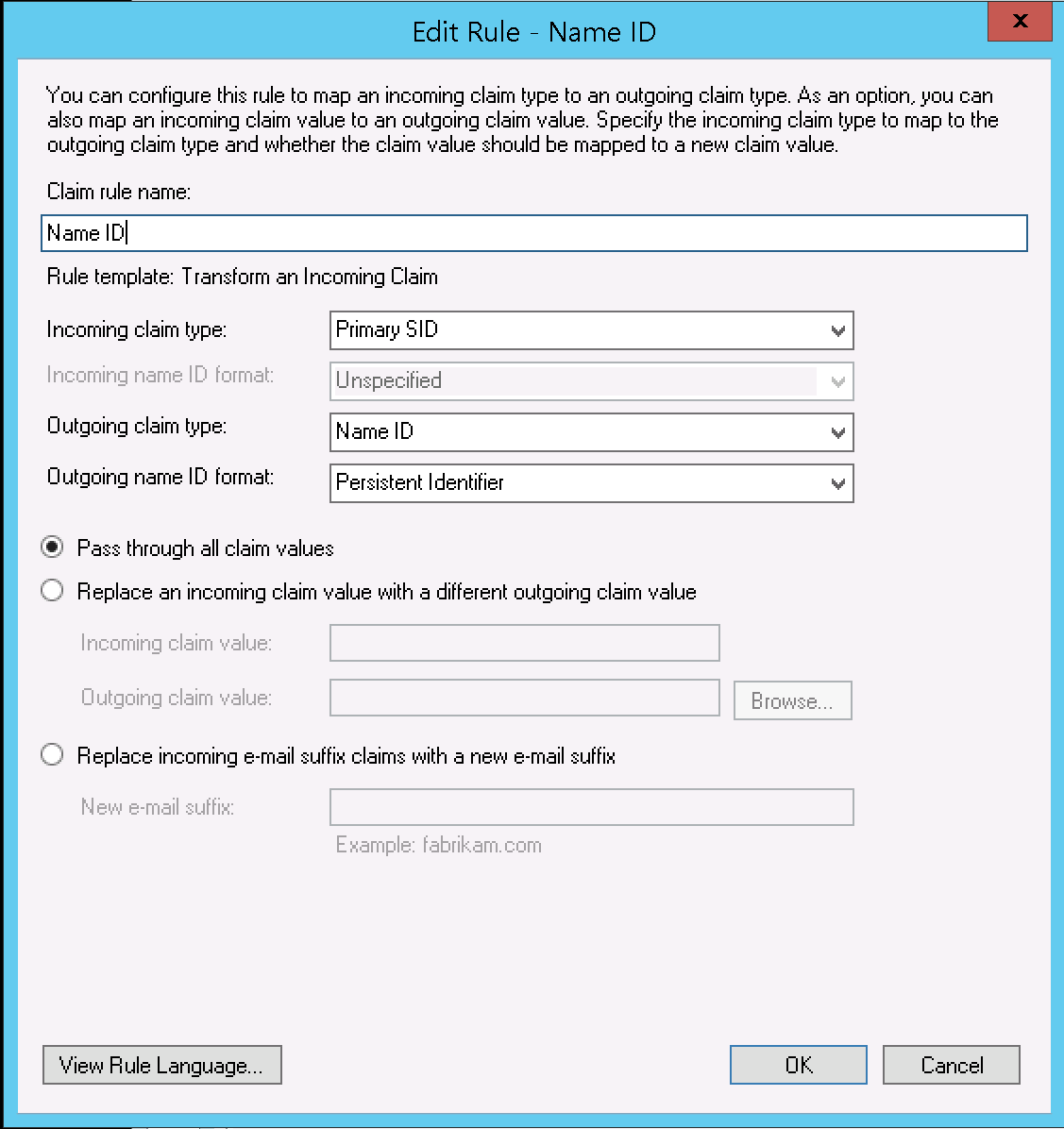
- Enter the following details:
- "Claim rule name" (highlighted in red, above): "Name ID"
- "Incoming claim type" (navy): "Common NamePrimary SID"
- "Outgoing claim type" (orange): "Name ID"
- "Outgoing name ID format" (green): "Persistent Identifier"
- Click "Finish".
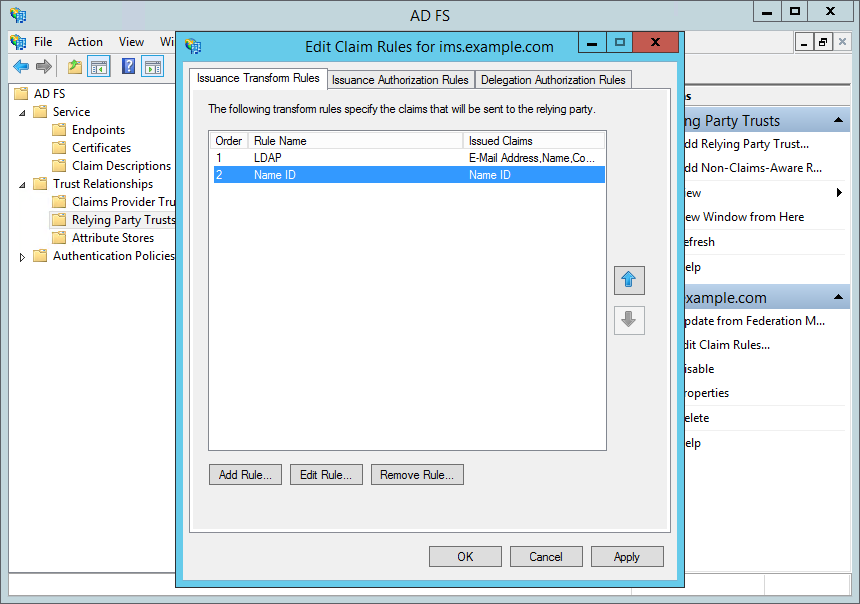
- Ensure that the order is "LDAP" and then "Name ID".
- Click "OK"
In the above, objectSid is used as the basis for generating a Name ID. You can use other fields - objectGuid being one suitable example. You should normally avoid using sAMAccountName / email / User Principal Name for this as they may change.
Testing the Configuration
...